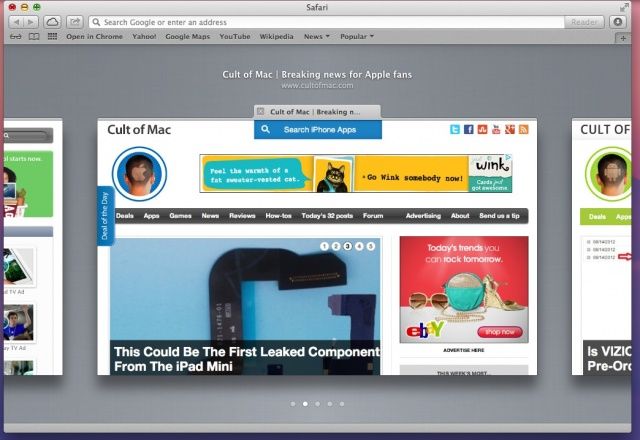
Safari Mac Mountain Lion
For the protection of our customers, Apple does not disclose, discuss, or confirm security issues until a full investigation has occurred and any necessary patches or releases are available. To learn more about Apple Product Security, see the Apple Product Security website.
Wild Safari North American Wildlife Mountain Lion (Male) Visit the Safari Ltd. 4.7 out of 5 stars 112 ratings. Make sure this fits by entering your model number. The largest of the small cat species, male mountain lions can grow up to 6 feet long and weigh 220 pounds. They have powerful hind legs and can jump.
For information about the Apple Product Security PGP Key, see How to use the Apple Product Security PGP Key.
Where possible, CVE IDs are used to reference the vulnerabilities for further information.
- Upgrading to Mountain Lion. To upgrade to Mountain Lion you must have Snow Leopard 10.6.8 or Lion installed. Purchase a redemption code at the Online Apple Store: OS X Mountain Lion. Mountain Lion is $19.99 plus tax. Use the code to redeem a download of Mountain Lion from the App Store. The file is quite large, over 4 GBs, so allow some time to.
- Official OS X Mountain Lion.app Installer from the Mac App Store. Both versions 10.8.4 AND 10.8.5 full installers included (zipped). Un-archive the zip archive and you will get the app Installer.
- Mac OS X Mountain Lion 10.8.5 is a very powerful and reliable operating system for your Macintosh computer with different enhancements and improvements. Mac OS X Mountain Lion 10.8.5 Review Apple has now released the Mac OS X 10.8.5 Mountain Lion release after a long beta period.
To learn about other security updates, see Apple security updates.
Safari 8.0.8, Safari 7.1.8, and Safari 6.2.8
Safari Application
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: Visiting a malicious website may lead to user interface spoofing
Description: A malicious website could open another site and prompt for user input without a way for the user to tell where the prompt came from. The issue was addressed by displaying the prompt origin to the user.
CVE-ID
CVE-2015-3729 : Code Audit Labs of VulnHunt.com
WebKit
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution
Description: Multiple memory corruption issues existed in WebKit. These issues were addressed through improved memory handling.
CVE-ID
CVE-2015-3730 : Apple
CVE-2015-3731 : Apple
CVE-2015-3732 : Apple
CVE-2015-3733 : Apple
CVE-2015-3734 : Apple
CVE-2015-3735 : Apple
CVE-2015-3736 : Apple
CVE-2015-3737 : Apple
CVE-2015-3738 : Apple
CVE-2015-3739 : Apple
CVE-2015-3740 : Apple
CVE-2015-3741 : Apple
CVE-2015-3742 : Apple
CVE-2015-3743 : Apple
CVE-2015-3744 : Apple
CVE-2015-3745 : Apple
CVE-2015-3746 : Apple
CVE-2015-3747 : Apple
CVE-2015-3748 : Apple
CVE-2015-3749 : Apple
WebKit
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: A malicious website may trigger plaintext requests to an origin under HTTP Strict Transport Security
Description: An issue existed where Content Security Policy report requests would not honor HTTP Strict Transport Security. This issue was addressed through improved HTTP Strict Transport Security enforcement.
CVE-ID
CVE-2015-3750 : Muneaki Nishimura (nishimunea)
WebKit
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: Image loading may violate a website's Content Security Policy directive
Description: An issue existed where websites with video controls would load images nested in object elements in violation of the website's Content Security Policy directive. This issue was addressed through improved Content Security Policy enforcement.
CVE-ID
CVE-2015-3751 : Muneaki Nishimura (nishimunea)


Download Os X Lion Installer
WebKit
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: Content Security Policy report requests may leak cookies
Description: Two issues existed in how cookies were added to Content Security Policy report requests. Cookies were sent in cross-origin report requests in violation of the standard. Cookies set during regular browsing were sent in private browsing. These issues were addressed through improved cookie handling.
CVE-ID
CVE-2015-3752 : Muneaki Nishimura (nishimunea)

WebKit Canvas
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: A malicious website may exfiltrate image data cross-origin
Description: Images fetched through URLs that redirected to a data:image resource could have been exfiltrated cross-origin. This issue was addressed through improved canvas taint tracking.
CVE-ID
CVE-2015-3753 : Antonio Sanso and Damien Antipa of Adobe

Mountain Lion Os X Download Free
WebKit Page Loading
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: Cached authentication state may reveal private browsing history
Description: An issue existed in caching of HTTP authentication. Credentials entered in private browsing mode were carried over to regular browsing which would reveal parts of the user's private browsing history. This issue was addressed through improved caching restrictions.
CVE-ID
CVE-2015-3754 : Dongsung Kim (@kid1ng)
Safari Mac Mountain Lion
WebKit Process Model
Available for: OS X Mountain Lion v10.8.5, OS X Mavericks v10.9.5, and OS X Yosemite v10.10.4
Impact: Visiting a malicious website may lead to user interface spoofing
Description: Navigating to a malformed URL may have allowed a malicious website to display an arbitrary URL. This issue was addressed through improved URL handling.
CVE-ID
CVE-2015-3755 : xisigr of Tencent's Xuanwu Lab